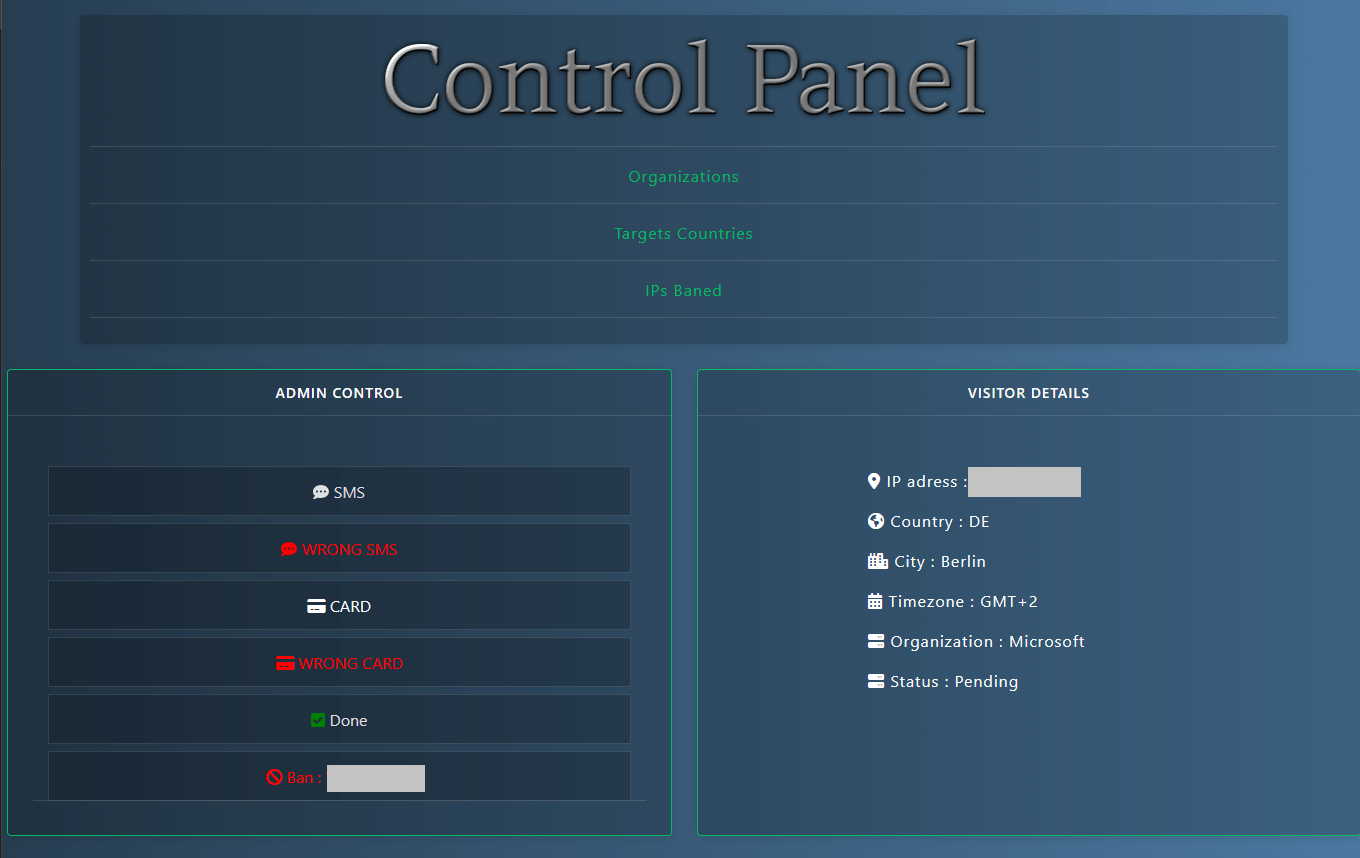
An example of an administration panel through which stolen data is managed.
Stolen data does not simply vanish after a phishing attack. According to new findings from Kaspersky, it embarks on a long and lucrative journey through underground markets, where it can be reused, repackaged, and weaponized against victims years after the initial breach.
Kaspersky reported that more than 117 million phishing links were clicked across the Asia-Pacific region in 2025 alone, all of which were detected and blocked by its security solutions. But not all users are protected, and phishing continues to rank among the most widespread cyber threats worldwide.
By impersonating trusted brands or services, attackers lure victims to fake websites where login credentials, personal information, and even bank card details are unknowingly handed over.
Tracing what happens next, Kaspersky experts uncovered a sophisticated ecosystem designed to collect, verify, and monetize stolen data at scale. Their analysis shows that 88.5 percent of phishing attacks are aimed at harvesting online account credentials, while 9.5 percent target personal information such as names, addresses, and birth dates.
The remaining 2 percent focus on bank card details, a smaller share but one that often carries immediate financial consequences.
Once stolen, the data is fed into automated management systems capable of handling massive volumes of information. These platforms, often offered as Platform-as-a-Service, are either custom-built by cybercriminals or adapted from legitimate website and application frameworks.
Through dedicated administration panels, attackers sort, validate, and prepare stolen details for resale or further exploitation.
According to Kaspersky Digital Footprint Intelligence, verified information is bundled into so-called “dumps,” which are then sold in bulk on dark web forums for as little as $50. Individual accounts with higher strategic value command steeper prices. Access to cryptocurrency platforms can sell for around $105, banking accounts average $350, e-government portals fetch about $82.50, while personal documents are typically priced at $15.
Before being sold, credentials are tested using automated scripts to confirm they still work, then combined with other leaked or publicly available data to form detailed digital profiles.
These enhanced “digital dossiers” significantly increase the value of stolen data, enabling more targeted and convincing attacks such as whaling schemes aimed at executives, public figures, or high-net-worth individuals. What begins as a single phishing mistake can therefore escalate into long-term exposure to identity theft, fraud, or blackmail.
“Stolen data evolves into a persistent weapon for cybercriminals,” said Olga Altukhova, security expert at Kaspersky. “By leveraging open-source intelligence and old breach data, attackers can craft highly personalized scams, turning one-time victims into long-term targets for identity theft, blackmail, or financial fraud.”
To reduce the risks posed by phishing-related data theft, Kaspersky advises users to immediately block compromised bank cards by contacting their financial institutions, change passwords on potentially affected accounts using unique combinations, and enable multi-factor authentication wherever possible.
Users are also urged to review active sessions in messaging apps, online banking platforms, and other services, and to rely on trusted security solutions that can protect devices and monitor for potential data leaks.
The full report detailing Kaspersky’s findings is available on Securelist.